The “why”
Some time ago I have written a post about obtaining a code signing certificate to sign your Revit DLLs and satisfy their requirement for plugins. That article is here. It was written in March of 2017 as Autodesk was introducing that pesky pop up for plugins that were not signed with a code signing certificate.

We all hated these pop ups and wanted to get rid of them. At the time of writing that post I was kind of piggy backing on the suggestion from Harry Mattison over at Boost Your BIM, that mentioned that he got his certificate from a company called K-Software, for 5 years at not so small cost of $365. I have since then been getting my certificates from K-Software via COMODO via SECTIGO. I know, it’s convoluted but they are all intermediaries. I think COMODO is the actual certification authority and K-Software and SECTIGO just sell that thing, and provide validation. Yes, validation. This is where we get to the point of this article. Over the last 5 years, I had to validate myself with SECTIGO a couple of times, as they no longer sell 5-year certificates. New regulations force them to issue code signing certificates for 2/3 years at most. That’s annoying as hell. If anyone had to go through that process, you know my pain. It’s a disaster. It probably shouldn’t be, but SECTIGO is such a shit company that they really managed to turn me away from something that I absolutely need to do my job. Yes, I am no longer getting my certificates from SECTIGO. If 5 years ago I said that I am not endorsing any particular company, then today, I am telling you to stay away from SECTIGO. Their validation process will make you want to throw your computer against the wall.
So what’s the alternative? I tried something called Certum which is a subsidiary of a Polish company called Asseco. I figured I speak Polish, so I can deal with their website and process not being completely translated to English. Be wary, it’s not. A lot of their videos and documents have plenty of Polish in it. Anyways, I got a certificate from them, and it turns out that it was a mistake too. Their validation process was a little better, but the certificate that they issue is locked into their proprietary software called SimplySign and you can only use it on your desktop computer. You don’t get your PFX/private key from them, so you would not be able to use it for example in GitHub as part of the release workflow. I described that process here. That’s a no go. I was getting a little fed up at this point.
What about creating my own certificate? I don’t think it matters all that much whether my Revit plugins are signed with a certificate that was issued by a 3rd party, that validated that my company exist, that I am a real person, etc. That’s all important and fine, but is it necessary for something as simple as code singing of Revit plugins to avoid pop ups? I think it’s time to stop paying these companies to put me through endless validation process, just so I can obtain from them something that I can get on my own in 5 minutes. Here’s how.
The “how”
Launch your Visual Studio as an Administrator.

Then go to Tools > Command Line > Developer Command Prompt

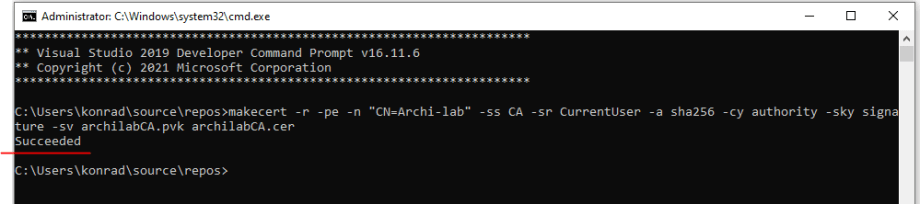
You should get this screen:

OK, now let’s type some code. The idea here is to do a few things:
- Create a Certificate Authority aka CA
- Save that CA into our certificate store
- Create a Code Signing certificate aka SPC
- Convert that code singing from PVK to PFX
That will prompt you with the following window asking for a password to your CA

Once you create that password you will get another prompt to now provide it

You should get a “Succeeded” message
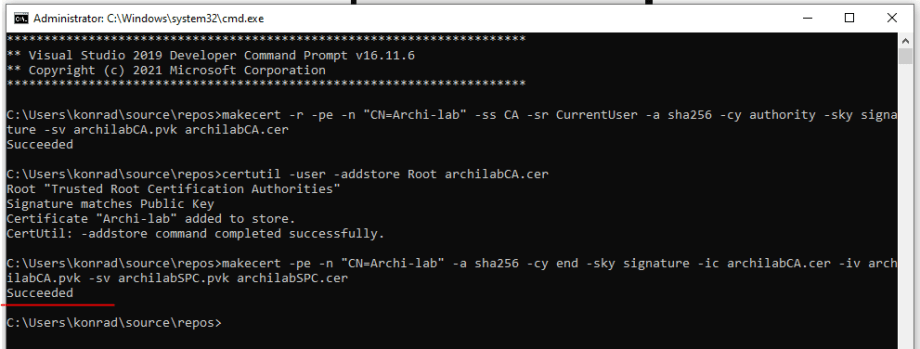
OK, now let’s install that Certificate Authority for our current user. This will add it to the certificate store and make it a trusted certificate authority on your computer.
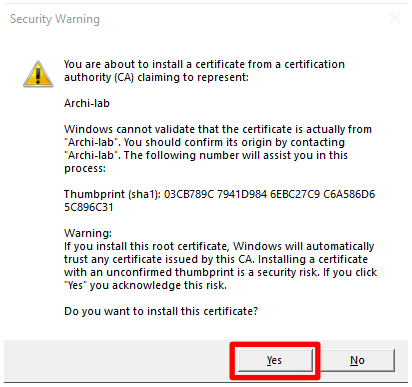
You will likely get a pop up asking you whether you trust that CA and really want to add it into your store. Click “Yes”.
Your command prompt will now show that the certificate was installed successfully.

Now we can use that CA to generate a Code Signing Certificate
Again, you will be asked to create a password for your Code Signing Certificate
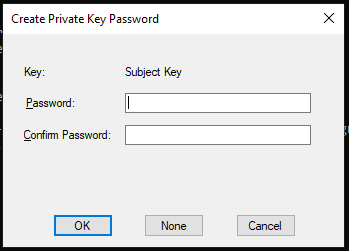
Then you will have to provide that same password like before

Only this time there is going to be a third pop-up asking for the CA password from the previous step. The CA is referred to as “Issuer” here.

If everything goes well, you should get the following message in your command prompt
So far so good. The last step here is to convert the Code Signing Certificate from the PVK format to PFX which we can then use locally or remotely in GitHub.
The “YOUR_PASSWORD” in the above command refers to a 3rd password. This is the PFX file password that protects the private key embedded in the file.
You will get a prompt to provide a password created in the second step. This is your Code Signing Certificate password.

Summary
That’s it! That should create your PFX file that you can now use with signtool, and code sign your Revit plugins for free! This self signed code signing certificate won’t expire for another 17 years so you should be good to go for a while.
Now, be aware of the fact that this self-signed code signing certificate is not the same as one issued to you by a 3rd party. I guess the level of “trust” here would be a little different, but in this particular case, I don’t think it matters to me. I am fed up with paying money to companies that have just atrocious customer support. If you are using these code signing certificates literally to just sign Revit plugins, then there is no reason to obtain one from a 3rd party and pay a hefty price for it on top of all the hoops that they will make you jump through.
I hope this helps some of the AEC development community out there save some money and time.
Cheers!














Nice post Konrad!
This was very helpful! Thank you!
Does this code signing also allows to sign installation executables or just Revit assemblies?
Luis, you can sign any file with it. I just want to stress the point that this code signing certificate is good enough for internal uses, or clients where you can get that certificate installed into their Trusted Root Store. In a typical commercial use case, you probably want an actual 3rd party verified certificate. Just FYI. Also, I am guessing that you want to avoid seeing the blue warning screen that MSIs usually spawn. For that one you need what 3rd party certificate authorities call extended verification. It costs extra but it will remove the blue screen from MSIs.
That microsoft…they don’t ship anymore makecert, so you have to find and install yourself (here’s the link: https://stackoverflow.com/questions/31772109/makecert-missing-from-windows-10-and-visual-studio-2015-install)
Thanks for sharing! I got mine shipped with Visual Studio though. If you pull up the command tool from VS, it works.
Hi Konrad,
Love what you all do!!
I get this warning: ‘makecert’ is not recognized as an internal or external command, operable program or batch file.
Please help me
Have to launch the command tool from within Visual Studio. Also, Fabio left a link to the tool itself since Microsoft doesn’t ship it with Windows.
thanks.but the customer doesn’t care what is displayed, they just cancel it.
Is there any way to completely cancel this pop-up window
Yes, I think I heard some companies take the certificate file, get it pre-installed into everyone’s root store, and then there is some field in a registry that can be set to completely avoid this pop-up. I am sorry I don’t have specifics but there are ways to get it done, but that would probably only work for an internal tool where IT is on board and wants to work with you on this. From your comment it sounds like it’s for a customer. That would probably be a little harder to pull off.
Konrad,
Excellent post. Very informative! Here is our story: Back in 2019 we contacted a vendor, who happen to be Comodo, to purchase a code signing certificate. We went with is vendor for cost reasons. Being a small company we have to pay close attention as the cost of our expenditures. Once the certificate was installed, I signed all of our software components and made it available to our clients. All was good till late 2021. When we rolled out a new release I realized that I have had failed to renew our certificate in time and subsequently contacted the vendor to do the renew process. This is when I got a big surprise. To renew our cert they, now being called Sectigo, required that the administrator of the cert send to them a copy of a government issued identification document. That is when I flat refused to comply with their request!! My supervisor questioned my hesitancy in doing this but I informed him that I would not give this information in any form to any entity online. So our policy to sign our software had been temporarily put on hold till this past month when a new release of our software product was ready to ship to our clients and I felt the subject should be discussed again with my supervisor. We have had discussions about the matter and resolution we agreed to was to use a 3rd party vendor that did not need to validate the administrator of the code signing cert.
So I agree with you that one should not do business with Sectigo!!
Kevin Kohler
Response Technology
Kevin,
Thank you for sharing your story. I am not sure if I would go that far as to say don’t do any business with them at all. I think my point was more like, if you do business with them, be ready for a lot of pain. For commercial software, there are other options available, granted at a higher price, but still better customer service than what Sectigo offers. My write up really is a great and cheap option for internal development teams that don’t ship commercial software, but rather develop it for internal use only. Why pay for code signing if the code is created in house, and you can create an in house certificate? Commercially though, you will run into friction with clients for not being validated by some 3rd party, or you won’t. It really depends on the kind of relationship you have with your clients. Anyways, thank you for sharing.
Cheers!
-K
Landed here searching for an alternative to Sectigo, after several weeks of validation process nightmare with them, all the way to paying for a lawyer certification letter following their template which they still rejected. Ready to give this a try.
Reading other sources though, think you’ll need to have the CA certificate installed in your user stores otherwise the pop-up will still show, just as a “not trusted company” instead of “unknown”
Nic,
This might be a good process for you, or it might not. It for sure makes no sense for a commercial application because you don’t have any control over the user stores. Like you said, you can create your own certificate but in order for it to be trusted it has to be installed into the trusted root store on end user computer. If you are developing internal plugins, you can work with your IT to get that sorted out, and then it’s a perfectly valid solution. If you are trying to sell some kind of commercial tool, you are not likely to be able to pre-install this into user store, and it’s still the same issue. The “real” value that these 3rd party companies like Sectigo offer, is that they issue certificates from a few publicly “trusted” companies like Comodo. So yes, your own self signed certificate is fine for personal use, or if you can get your IT to work with you. Otherwise, keep going with the commercial one.